 Officials in Jackson County, Georgia, have relented and paid a $400 000 ransom in bitcoins to restore county IT systems disabled by Ryuk ransomware since March 1st, Bank Info Security reports.
Officials in Jackson County, Georgia, have relented and paid a $400 000 ransom in bitcoins to restore county IT systems disabled by Ryuk ransomware since March 1st, Bank Info Security reports.
The FBI and local law enforcement are now investigating the attack.
Jackson County now joins numerous other public institutions hit by ransomware attacks in recent years.
The American Justice Department reportedly believes at least $6 million USD has been collected in these hacks.
Last December, operations at multiple newspapers owned by Tribune Publishing, including the New York Times and the Washington Post (West Coast editions), were disrupted by a Ryuk ransomware attack.
Newark, New Jersey; the Colorado Department of Public Transportation; the Port of San Diego; hospitals and the Boston public defenders office have all been hit by ransomware attacks in the past year.
Fortunately, the Boston Committee for Public Counsel Services’ systems and files were backed up and it was able to refuse to pay a ransom in after its systems succumbed to a Ryuk ransomware attack deployed against it in earlier this year.
Still, the attack resulted in weeks-long delays of certain court cases, including a case of alleged sexual assault against a child.
The committee’s IT staff are now undertaking weeks of work trying to clear all vestiges of the ransomware and the Trojan virus used to install it on their systems.
But the Jackson County attack appears to have had a more severe effect.
While police communications and 911 services in the county remained online and functional, records at the county jail and elsewhere have had to be filled in by hand.
The county took to social media to inform the public that its email systems were down and advised citizens to contact them by phone.
Recovering from these attacks can be a lengthy process and can cost additional man-hours.
McAfee head of cyber investigations John Fokker reportedly claims that, after a ransom is paid Ryuk hackers, the decoder they provide may only restore the files in a jumbled way, meaning IT department workers have spent weeks sorting them.
ZDNet has reported that Ryuk ransomware appears to be being spread by financially-motivated professional hack groups in Russia.
While some researchers believe that Ryuk is being spread by gangs and not by Russian authorities, Ryuk has also reportedly been made available on Dark Net marketplaces with the caveat that it not be used against targets in Russia or former Soviet republics.
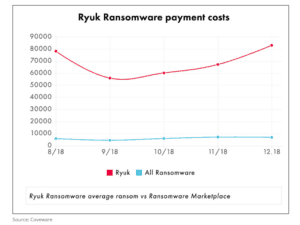
According to cybersecurity firm Coveware, Ryuk appears to be the most profitable of all ransomware campaigns to date:
A person commenting on the attack on the Boston public defence system said hackers are likely targeting public institutions because they often have less money to devote to cybersecurity.
Private businesses, including a private heart clinic in Australia, have also been targeted in ransomware attacks.
Bill Seigel, CEO of Coveware, has described Ryuk as potentially “fatal” to a private business with time-sensitive data needs:
“Because of the extremely high ransom demands, and highly problematic decryption tool, a Ryuk attack can be fatal to a business that is intolerant of downtime and does not have easily restored backups.”

