 Microsoft has found that ransomware and cryptomining hackers are finding the most success in Ethiopia, Cameroon, Tanzania and Zambia, while the UAE, South Africa and Namibia have proven themselves as the most secure nations in Africa and the Middle East when it comes to repelling cryptocurrency-motivated hacks.
Microsoft has found that ransomware and cryptomining hackers are finding the most success in Ethiopia, Cameroon, Tanzania and Zambia, while the UAE, South Africa and Namibia have proven themselves as the most secure nations in Africa and the Middle East when it comes to repelling cryptocurrency-motivated hacks.
Microsoft presented the findings in its 2018 Security Intelligence Report (SIR). The company reportedly analyzed over 6.5 trillion “daily threat signals” to produce the report.
All told, the signals painted a welcome picture of a 73% decline in ransomware attacks.
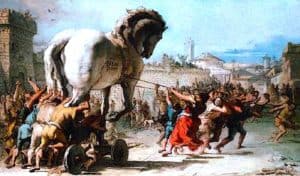
Ransomware attacks are a very stressful and potentially costly type of hack whereby attackers fool employees and key individuals into clicking on infected attachments in phishing emails.
Once clicked, those attachments load Trojan and other malware onto networked computer systems at companies and public institutions.
The malware thereafter works to lock down (encrypt) important or sensitive data.
Once the data is encrypted, hackers usually demand a ransom in cryptocurrency to unlock and or return the data.
Businesses and numerous public service branches across the world have had to spend days or weeks restoring computer systems and meticulously removing malware and Trojans. Failing to do so could result in a reactivated attack.
Malware phishing email attacks may be targeted or just randomly and voluminously deployed.
According to Microsoft:
“(L)ow ransomware encounter rate countries are known to communicate with their citizens about basic security. Countries with lowest ransomware encounter rates also have mature cybersecurity infrastructures and well-established programmes for protecting critical infrastructure.”
The company says that countries least affected by ransomware attacks in 2018 were Ireland (0.01), Japan (0.01), the United States (0.02), United Kingdom (0.02), and Sweden (0.02 percent).
The overall decline in ransomware attacks has unfortunately been accompanied by a concurrent increase in cryptocurrency mining attacks, which can be executed “in the background” and can go undetected for some time.
Cryptocurrency mining attacks may also be proliferated by phishing emails or by infected links at popular websites.
Unlike ransomware, however, cryptomining malware will not lock down systems.
It may rather “lock open” systems and prevent them from sleeping so that they may be engaged in the expensive process of mining for cryptocurrencies 24-hours-a-day.
Wildly expensive mining energy costs are then paid for by the affected company or public service, and all proceeds of mining sent to attackers.
African countries are also the most affected by this newly-preferred form of hack, says Microsoft:
“(In the) Middle East and Africa, cryptocurrency mining is particularly prevalent. Ethiopia, Tanzania and Zambia account for three of the top five nations most impacted by cryptocurrency mining. With encounter rates well above the global average at 5.58, 1.83 and 1.13 % respectively.”
Besides ensuring that a company or institution is subscribed to good anti-malware and anti-virus services, the best way to prevent these attacks to to train employees to be very wary of clicking attachments, even if they seem to have originated from a known source.

