 Eight “potentially unwanted applications” (PUAs) identified by cybersecurity researchers at Symantec have been now been removed from the Microsoft Store.
Eight “potentially unwanted applications” (PUAs) identified by cybersecurity researchers at Symantec have been now been removed from the Microsoft Store.
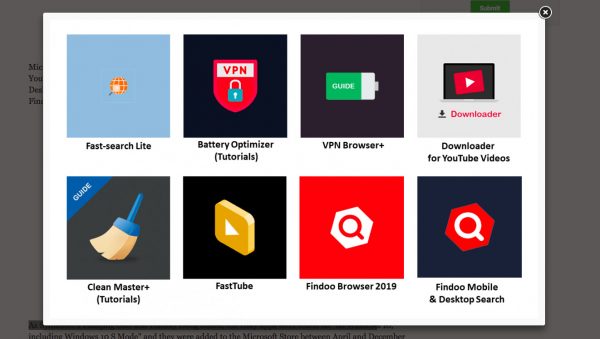
The eight fake apps -Fast-search Lite, Battery Optimizer (Tutorials), VPN Browsers+, Downloader for YouTube Videos, Clean Master+ (Tutorials), FastTube, Findoo Browser 2019, and Findoo Mobile & Desktop Search- are all designed to drop a payload of malicious Monero (XMR) Coinhive cryptomining software onto computers of unsuspecting downloaders.
According to Bleeping Computer, the apps reportedly exploit, “a tag management system designed by Google to help developers inject JavaScript and HTML content within their apps for tracking and analytics purposes.”
But soon after they are deployed, these malicious apps work to “zombify” infected systems and engage them in a process called “cryptojackng” where infected computers’ processing powers are commanded for the mining of Monero crypto coins to profit malware pervaders:
“Criminals will collect all the cryptocurrency surreptitiously mined using compromised systems and send it crypto wallets which they control.”
Symantec writes:
“As soon as the apps are downloaded and launched, they fetch a coin-mining JavaScript library by triggering Google Tag Manager (GTM) in their domain servers. The mining script then gets activated and begins using the majority of the computer’s CPU cycles to mine Monero for the operators. Although these apps appear to provide privacy policies, there is no mention of coin mining on their descriptions on the app store.”
The apps all appear to have been created by the same three developers: DigiDream, 1clean, and Findoofrom.
Symantec adds that the malicious software could affect GPU performance:
“Seeing that cryptomining scripts will most of the time run on the compromised machines without any sort of resource usage controls, it is very possible that the Windows systems where these particular apps landed were experiencing serious performance issues because of continuously using all CPU resources to mine Monero for their masters.”
Cryptomining malware has also been known to run down affected systems and run up electricity bills.
Check Point Research, has claimed that cryptominer infections were ten-times more common in 2018 than ransomware infections.
Meanwhile, only 20% of cybersecurity professionals are reportedly adept at detecting these surreptitious infections, which have often been used to target large commercial computer systems.

