The US Department of Justice has announced an indictment of three North Korean hackers said to be involved with the Korean military regarding to cyberattacks and financial including theft of money and cryptocurrency. The indictment is an expansion of a 2018 case outlining similar nefarious actions.
The theft of money and cryptocurrency from financial institutions and companies was said to include multiple malicious cryptocurrency applications, as well as the development and fraudulently market a blockchain platform.
A second case involved a Canadian-American citizen that has pleaded guilty to money laundering while admitting to being a money launderer for “multiple criminal schemes, including ATM “cash-out” operations and a cyber-enabled bank heist orchestrated by North Korean hackers.” Ghaleb Alaumary, 37, of Mississauga, Ontario, Canada, was charged for his role as a money launderer for the North Korean actions, among other criminal activities. Alaumary has agreed to plead guilty to one count of conspiracy to commit money laundering, which carries a maximum sentence of 20 years in prison.
Alaumary was said to have organized teams of co-conspirators in the United States and Canada to launder millions of dollars obtained through ATM cash-out operations, including from BankIslami and a bank in India in 2018. Alaumary also conspired with Ramon Olorunwa Abbas, aka “Ray Hushpuppi,” and others to launder funds from a North Korean-perpetrated cyber-enabled heist from a Maltese bank in February 2019. Last summer, Abbas was charged in a separate case.
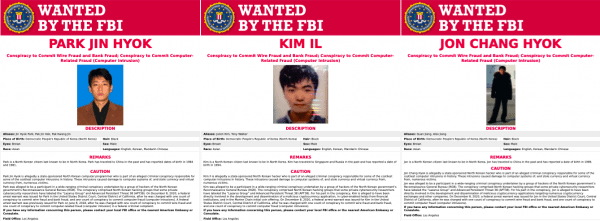
The hacking indictment filed in the U.S. District Court in Los Angeles alleges that Jon Chang Hyok (전창혁), 31; Kim Il (김일), 27; and Park Jin Hyok (박진혁), 36, who are said to be members of units of the Reconnaissance General Bureau (RGB), a military intelligence agency of the Democratic People’s Republic of Korea (DPRK), which engaged in criminal hacking. Jon, Kim, and Park are charged with one count of conspiracy to commit computer fraud and abuse, which carries a maximum sentence of five years in prison, and one count of conspiracy to commit wire fraud and bank fraud, which carries a maximum sentence of 30 years in prison.
The DOJ said these North Korean military hacking units are known by multiple names including Lazarus Group and Advanced Persistent Threat 38 (APT38).
Assistant Attorney General John C. Demers of the Justice Department’s National Security Division, stated:
“As laid out in today’s indictment, North Korea’s operatives, using keyboards rather than guns, stealing digital wallets of cryptocurrency instead of sacks of cash, are the world’s leading bank robbers. The Department will continue to confront malicious nation state cyber activity with our unique tools and work with our fellow agencies and the family of norms abiding nations to do the same.”
FBI Deputy Director Paul Abbate said the cyber-enabled theft was met with the “outstanding, persistent investigative efforts of the FBI in close collaboration with U.S. and foreign partners:”
“By arresting facilitators, seizing funds, and charging those responsible for the hacking conspiracy, the FBI continues to impose consequences and hold North Korea accountable for its/their criminal cyber activity.”
The indictment alleges:
- Cyberattacks on the Entertainment Industry: The destructive cyberattack on Sony Pictures Entertainment in November 2014 in retaliation for “The Interview,” a movie that depicted a fictional assassination of the DPRK’s leader; the December 2014 targeting of AMC Theatres, which was scheduled to show the film; and a 2015 intrusion into Mammoth Screen, which was producing a fictional series involving a British nuclear scientist taken prisoner in DPRK.
- Cyber-Enabled Heists from Banks: Attempts from 2015 through 2019 to steal more than $1.2 billion from banks in Vietnam, Bangladesh, Taiwan, Mexico, Malta, and Africa by hacking the banks’ computer networks and sending fraudulent Society for Worldwide Interbank Financial Telecommunication (SWIFT) messages.
- Cyber-Enabled ATM Cash-Out Thefts: Thefts through ATM cash-out schemes – referred to by the U.S. government as “FASTCash” – including the October 2018 theft of $6.1 million from BankIslami Pakistan Limited (BankIslami).
- Ransomware and Cyber-Enabled Extortion: Creation of the destructive WannaCry 2.0 ransomware in May 2017, and the extortion and attempted extortion of victim companies from 2017 through 2020 involving the theft of sensitive data and deployment of other ransomware.
- Creation and Deployment of Malicious Cryptocurrency Applications: Development of multiple malicious cryptocurrency applications from March 2018 through at least September 2020 – including Celas Trade Pro, WorldBit-Bot, iCryptoFx, Union Crypto Trader, Kupay Wallet, CoinGo Trade, Dorusio, CryptoNeuro Trader, and Ants2Whale – which would provide the North Korean hackers a backdoor into the victims’ computers.
- Targeting of Cryptocurrency Companies and Theft of Cryptocurrency: Targeting of hundreds of cryptocurrency companies and the theft of tens of millions of dollars’ worth of cryptocurrency, including $75 million from a Slovenian cryptocurrency company in December 2017; $24.9 million from an Indonesian cryptocurrency company in September 2018; and $11.8 million from a financial services company in New York in August 2020 in which the hackers used the malicious CryptoNeuro Trader application as a backdoor.
- Spear-Phishing Campaigns: Multiple spear-phishing campaigns from March 2016 through February 2020 that targeted employees of United States cleared defense contractors, energy companies, aerospace companies, technology companies, the U.S.Department of State, and the U.S. Department of Defense.
- Marine Chain Token and Initial Coin Offering: Development and marketing in 2017 and 2018 of the Marine Chain Token to enable investors to purchase fractional ownership interests in marine shipping vessels, supported by a blockchain, which would allow the DPRK to secretly obtain funds from investors, control interests in marine shipping vessels, and evade U.S. sanctions.
Simultaneously, the FBI and the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency, in collaboration with the U.S. Department of Treasury, today released a joint cybersecurity advisory and malware analysis reports (MARs) regarding North Korean cryptocurrency malware. The joint cybersecurity analysis and MARs highlight the cyber threat North Korea – which is referred to by the U.S. government as HIDDEN COBRA – poses to cryptocurrency and identify malware and indicators of compromise related to the “AppleJeus” family of malware (the name given by the cybersecurity community to a family of North Korean malicious cryptocurrency applications that includes Celas Trade Pro, WorldBit-Bot, Union Crypto Trader, Kupay Wallet, CoinGo Trade, Dorusio, CryptoNeuro Trader, and Ants2Whale). The joint cybersecurity advisory and MARs collectively provide the cybersecurity community and public with information about identifying North Korean malicious cryptocurrency applications, avoiding intrusions, and remedying infections.
The U.S. Attorney’s Office and FBI has obtained seizure warrants authorizing the FBI to seize cryptocurrency stolen by the North Korean hackers from a victim in the indictment, a financial services company in New York, held at two unnamed cryptocurrency exchanges. The seizures include sums of multiple cryptocurrencies totaling approximately $1.9 million, which will be returned to the unnamed victim.