For all the joy that quick online banking can provide, it can also cause a lot of headaches if your account is compromised. Berlin-based fintech company N26 (short for Number26) was accused of numerous security flaws late last year that could have been used to defraud thousands of users, according to a Reuters report on a University of Erlangen-Nuernberg Computer Science Department project. N26 said that they have quickly repaired the flaws.
Research fellow and CS PhD student at the University of Erlangen-Nuernberg Vincent Haupert explained last month that N26’s security defenses did not provide adequate user protection from fraud.

“They say you can open a bank account in just eight minutes. As it turns out, you can lose it even faster. …With such a strategy, fintechs squander the trust that banks established over years.”
Reuters covered Haupert’s explanation at the Chaos Communications Congress (C3) conference in Hamburg last month;
“Haupert said he compared data from a leak of 68 million account credentials from online file sharing company Dropbox with information on N26 users he was able to request from the company’s own software feed to identify 33,000 N26 user credentials – without being thwarted by N26 anti-fraud systems.
From there, he said it would have been simple to send a phishing email to these N26 customers that could potentially have allowed him to break into their accounts.”
Haupert and his co-researchers did not carry out the hacking attempts though, thinking about the legal consequences.
After Haupert disclosed his research findings to N26 in September, the startup said that it “immediately started to assess the scope and the impact of the demonstrated method.” N26 also told its users;
“Our comprehensive tests have determined that our customers’ personal information was never exposed to third parties in any of the evaluated scenarios. We were also unable to find any evidence of non-authorized transactions that were committed through this method.
This means that the personal data and the funds of N26 users were not impacted by the demonstrated vulnerability. N26 Users do not need to take further action in order to secure their accounts.
As a result of our investigation, we have identified and fixed all potential vulnerabilities demonstrated by this method prior to it becoming public knowledge.”
Haupert and his team in turn responded;
“All vulnerabilities have been disclosed responsibly to N26 on September 25, 2016.
As of December 13, to the best of our knowledge, all vulnerabilities that we have reported to N26 are closed. Therefore, we are confident that the 33c3 talk will not do damage to any N26 customer. We want to emphasize and commend the responsive and friendly contact with N26.”
N26 averted a security breach disaster during a year full of them. Haupert’s team research and N26’s quick repairs stand as a lesson for companies to constantly keep its products updated and to take security seriously.
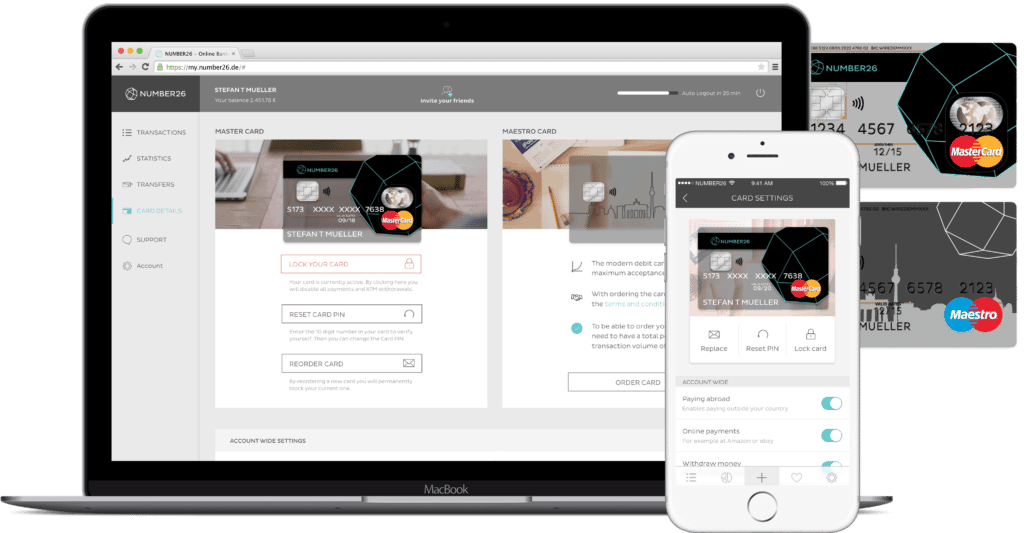
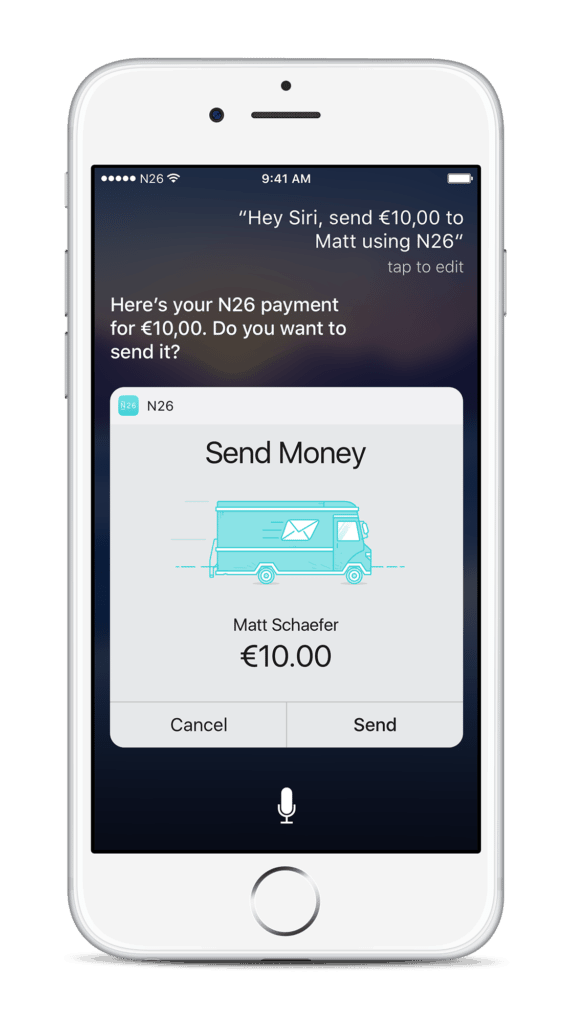
N26 was founded in 2013 and touted its smartphone-only banking services to separate itself from traditional banks. It is backed by Silicon Valley giant Peter Thiel.

