Blockchain data analysis firm Elementus has published stunning claims regarding last week’s hack on the New Zealand Cryptopia cryptocurrency exchange.
Little information regarding the scope or nature of the attack has so far been issued by Cryptopia itself or New Zealand police.
Two days ago, in the name of “overdue transparency,” Elementus claimed that for four days straight, Cryptopia operators watched as more than 76 000 Cryptopia hot wallets were accessed and drained of ethers and Ethereum-based tokens worth $16 million.
The exchange not only lost the keys that opened the accounts, but they were also unable to turn off the taps.
Elementus arrived at this conclusion by studying transactions recorded on the Ethereum blockchain.
Elementus did not analyze the Bitcoin blockchain for Cryptopia-hack activity, suggesting that even more may have been lost there.
Attackers, says Elementus, first went after Cryptopia’s “core” pools of crypto being stored in company “hot wallets” accessible online:
- “Sunday 13-Jan, 8:28am: Funds begin moving out of Cryptopia’s two core hot wallets, one holding ether and the other holding tokens.”
Hackers then went after “secondary” hot wallets, possibly customer wallets, managed by the exchange:
- “Sunday 13-Jan, 11:58pm: With the core wallets empty, residual quantities of funds begin leaving Cryptopia’s 76k+ secondary wallets, a process that would continue for several days.”
The next day, Cryptopia reportedly discovered the hack and suspended trading, announcing publicly that it was undergoing “unscheduled maintenance.”
Cryptopia told the public about the hack on Tuesday, January 15th, says Elementus, the same day that police arrived on the scene:
- “Tuesday 15-Jan, 3:00am: Cryptopia discloses the security breach and New Zealand law enforcement steps in.”
Even with the help of law enforcement, funds continued to move off the exchange until Thursday, January 17th, Elementus says:
- “Thursday 17-Jan, 5:58am: The last of Cryptopia’s funds are drained.”
 Typical exchange hacks, says the company, usually involve a “smart contract” exploit where a weak piece of code is used to unlock funds in crypto “hot wallet.”
Typical exchange hacks, says the company, usually involve a “smart contract” exploit where a weak piece of code is used to unlock funds in crypto “hot wallet.”
Other typical hacks involve the theft of an individual’s “private keys,” alphanumeric strings of characters used to unlock crypto balances and allow them to be transferred.
According to Elementus, “the Cryptopia hack differs from these profiles in two glaring ways”:
- “The Cryptopia hack involved a large number of wallets. The funds were taken from more than 76k different wallets, none of which were smart contracts. The thieves must have gained access to not one private key, but thousands of them (italics added).”
- “The hack continued for days after Cryptopia discovered the breach. The lack of urgency on the part of the thieves is striking. Rather than withdrawing the funds as fast as possible, as is the case in most crypto hacks, they took their time extracting the assets over the course of nearly five days (italics added).”“After Cryptopia discovered the hack, they watched the funds continue to flow out of their wallets for four more days, seemingly powerless to stop it. As these wallets were not smart contracts, there should have been no technical complications preventing Cryptopia from securing the funds.”
Elementus arrives at the conclusion that Cryptopia not only lost thousands of private keys, it also lost control of its wallets:
“It seems Cryptopia not only lost their funds, they also lost access to all, or nearly all, of their 76k+ Ethereum wallets.”
For this exploit to work, says Cryptopia, the exchange may have, “…had their private keys stored in a single server with no redundancy”:
“If the thieves managed to gain access to this server, they could have downloaded the private keys before wiping them from the server, leaving Cryptopia unable to access their own wallets.”
Attackers have been moving funds stolen from Cryptopia to 13 other exchanges, including Kucoin, HitBTC, Bibox, Binance, Bittrex and Huobi.
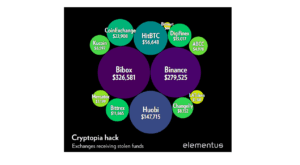
Regarding this, Cryptopia states:
“Exchanges should be freezing these funds as soon as they arrive. No excuses. On the blockchain there is nowhere to hide, and no reason 100% of these transfers should not have been frozen immediately…Any exchanges who care about compliance and want to block these illicit funds are encouraged to get in touch.”


